Blockchain Anchor
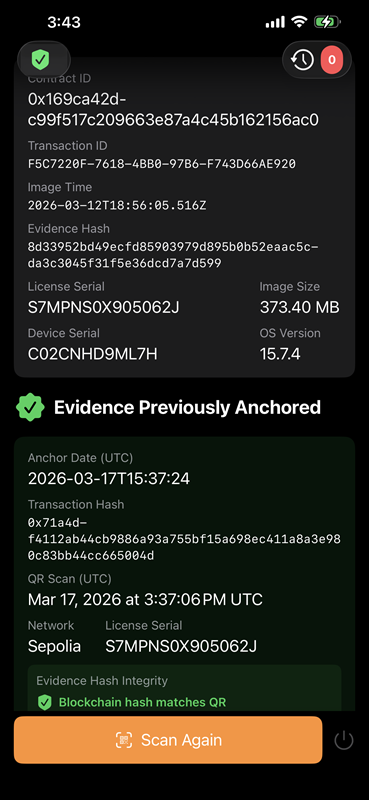
The shift toward blockchain-anchored forensics often raises immediate concerns regarding data privacy and the exposure of sensitive litigation materials. However, the LLSmartVerify™ framework is engineered with a "privacy-by-design" philosophy that fundamentally separates the verification of the event from the contents of the evidence. By anchoring only the salted cryptographic fingerprints—or hashes—of an image to the blockchain, we create a permanent notarization of the collection without ever uploading the actual file. This ensures that while the integrity of the evidence is anchored to a global ledger, the data itself remains entirely within your secure, AWS air-gapped, or encrypted environment, far removed from the public domain.
In this architecture, the blockchain acts as a digital witness rather than a storage locker. When LLIMAGER completes an acquisition, it generates a one-way cryptographic hash that represents the unique state of the DMG file. This hash is a mathematical string that is impossible to reverse-engineer; it cannot be used to reconstruct the original data or even reveal its file name or size. Because only this anonymous signature is submitted to the ledger, your organization maintains a "Zero-Knowledge" proof of integrity. You can prove to any court that the evidence existed in an exact state at an exact second, while ensuring that the public ledger contains no readable or exploitable information about the actual subject matter.
This separation of data and metadata is the ultimate defense against the security risks associated with cloud-based forensic repositories. In legacy systems, storing logs or evidence in a central portal often creates a high-value target for breach; in our ecosystem, even a total compromise of the public ledger would yield nothing but a list of mathematical signatures. Your sensitive clear-text data never crosses the boundary of your secure forensic workstation or your mobile companion app. This allows government agencies and law firms to meet the most stringent data-sovereignty requirements, as the "Source of Truth" remains local and private, while the "Certificate of Authenticity" is decentralized and indestructible.
Ultimately, this privacy-first approach transforms how forensic evidence is presented in the courtroom. By providing a publicly verifiable anchor that contains no clear-text data, you enable a process of "Democratic Verification." A Judge or opposing counsel can verify the timestamp and the file’s integrity using a public portal, yet they are never granted access to the underlying data through that portal. This creates a transparent, self-authenticating chain of custody that satisfies the court’s need for mathematical certainty while upholding the examiner’s duty to protect the privacy and confidentiality of the evidence throughout the life of the matter.