Acquisition Log
The Initial Acquisition State captured by LLIMAGER v6 represents the critical "Point of Origin" for the entire forensic lifecycle. Unlike legacy tools that simply copy files, LLIMAGER v6 performs a comprehensive environmental audit of the target Mac at the millisecond the imaging process begins. This initial state doesn't just record the file contents; it captures the volatile system metadata, hardware identifiers, and internal clock settings, wrapping them into a secure, preliminary log. This creates a "gold master" record of the machine’s condition before a single bit of evidence is processed, ensuring that the starting line of your chain of custody is documented with absolute precision.
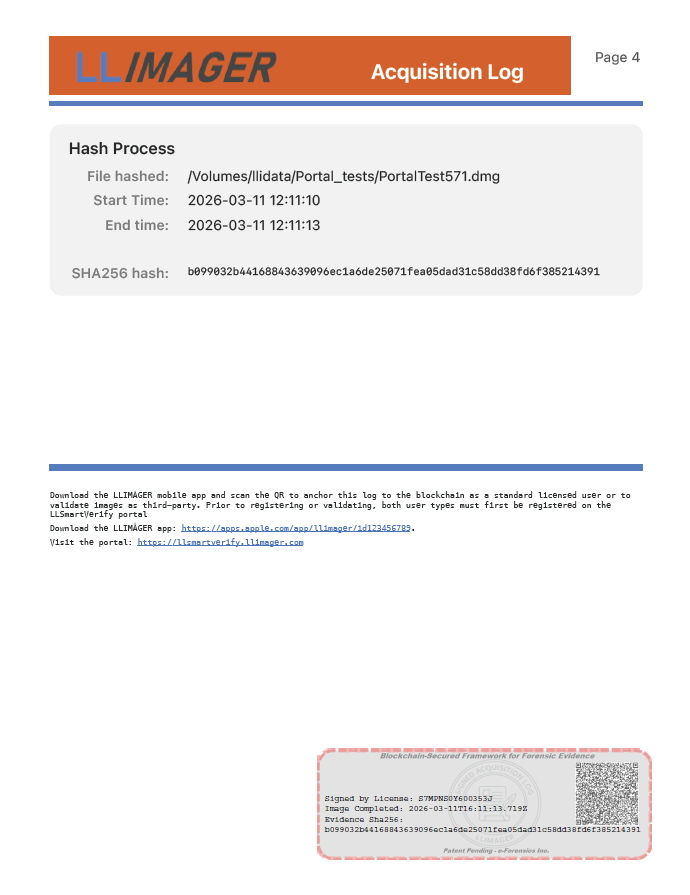
The innovation of the Metadata QR Code transforms this acquisition state from a static text file into an interactive forensic trigger. Once the initial state is captured, LLIMAGER v6 generates a high-density, encrypted QR code directly on the imaging screen. This code acts as a physical manifestation of the digital metadata, containing the unique cryptographic signature of the acquisition log. By projecting this data as a machine-readable code, we eliminate the need for technicians to manually export, rename, or type out complex hash values—processes that are notoriously prone to human error and "typo-spoliation" in high-pressure field environments.
When the mobile companion app interacts with this QR code, it performs a "Digital Handshake" that effectively locks the acquisition state in time. The QR code serves as the secure hand-off point, transferring the machine’s internal metadata to the mobile device's carrier-synced environment. This step is vital because it proves that the examiner was physically present and in direct control of the target Mac. By scanning the code, the examiner "witnesses" the initial state, marrying the Mac’s internal data to the external network time and GPS coordinates. This creates a forensic "event" that is far more difficult to challenge than a simple file transfer.
Ultimately, this QR-driven acquisition process ensures that the Foundation of Evidence is unshakeable from the very first step. In a courtroom, an examiner can demonstrate that the metadata was not "added later" or "edited in post-production." Because the QR code was generated based on the initial state and scanned immediately in the field, the integrity of the data is established at the source. This workflow replaces the archaic "side-car text file" with a dynamic, cryptographic link, ensuring that the image’s journey from the target Mac to the blockchain begins with a verified, machine-authenticated starting point.